Weak password settings leave IoT devices vulnerable to attack
By successfully hacking IoT devices, criminals are able to blackmail people or spy on them.
Imagine that you wanted to treat your child and so decided to buy him an amazing smart app-controlled wireless spy vehicle — essentially a spy camera on wheels, connected via Wi-Fi and managed via a mobile application. It is truly an amazing present that allows him to not only drive it around but also take photos, record videos and even play audio remotely via a built-in speaker. Not to mention the fact that it was Cyber Monday so you were able to get it at a bargain price!
It was perfect to get you in the festive mood, but several days after purchasing the vehicle you suddenly started to notice that something was wrong and the vehicle went out of control. It appeared to be obeying someone else’s commands, record video you did not want and lose charge unexpectedly fast. How did this happen? Most likely, it is because you bought a vulnerable and insecure gift.
Connected smart devices are generally considered to be a very convenient way to make our lives easier. But to what extent are they safe to use from a cybersecurity point of view? In 2015, Kaspersky Lab researchers decided to examine the severity of the threat behind the Internet of Things (IoT). The results were concerning, so two years later they conducted more research into the area. Of eight randomly selected IoT devices – ranging from a smart iron to a smart spy vehicle — half were hackable due to weak password settings. Moreover, only one device satisfied the researchers’ requirements and proved to be secure.
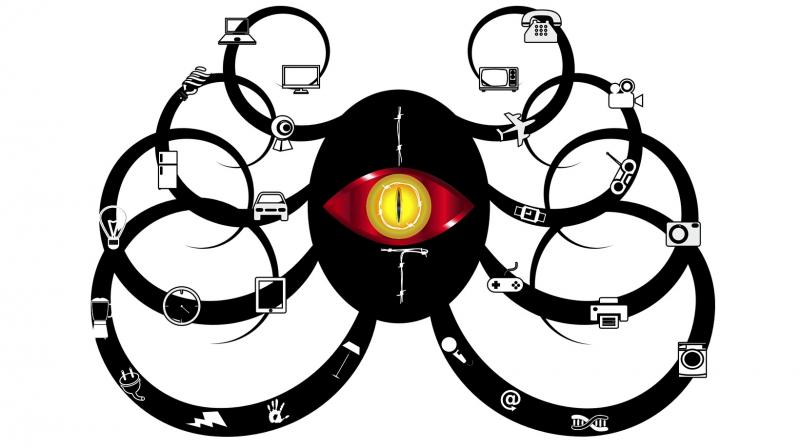
IoT devices are basically devices with network connectivity – equipped with embedded technology that allows them to interact with each other or the external environment. Because of the large number and variety of devices available, the IoT has become an attractive target for cybercriminals. This includes, among others, the record-breaking DDoS attacks of 2016 that were launched with the help of a massive botnet made up of routers, IP cameras, printers and other devices. By successfully hacking IoT devices, criminals are able to blackmail people or spy on them. Other vectors can be even more dangerous. For example, your home network devices could be used to perform illegal activities, or a cybercriminal who has gained access to an IoT device could blackmail — and spy on — its owner or extort money from him. The infected device can also simply be broken, though clearly, this is by no means the worst thing that can happen.
With this in mind, researchers at Kaspersky Lab decided to find out whether the reports on smart ‘IoT’ products and the incidents that have occurred have changed the security situation. To uncover the answer, they once again analysed several randomly selected smart devices, consisting of a smart charger, an app-controlled toy car, smart receivers, a smart scale, a smart cleaner, a smart iron, a smart camera and a smartwatch. The findings were truly worrying: of the eight examined devices, only one satisfied the researchers’ security requirements.
What’s more, half of the devices could be compromised and simply exploited due to a lack of vendor vigilance in the password settings. This included having a default password and an inability to change the password, while in some cases the password was even unified for all devices in the product line.
“At Kaspersky Lab, we have been monitoring the issue of smart devices’ cybersecurity for years. We are now seeing that various reports on smart ‘IoT’ products and increasing levels of vendor vigilance have helped to decrease the volume of insecure smart devices. However, the problem is still there and smart devices still can bring harm to their owners, indicating that there is much more work to be done jointly by cyber security firms and vendors of connected devices,” notes Oleg Zaitsev, a security expert at Kaspersky Lab.
Therefore, it is advised to take the following measures in order to protect themselves from buying vulnerable smart devices:
1. Before buying an IoT device, search the Internet for news of any vulnerability. It is likely that the device you are going to purchase has been already examined by security researchers and it is often possible to find out whether the issues found in the device have been patched or not.
2. It is not always a good idea to buy the most recent products released on the market. Along with the standard bugs commonly found in new products, recently-launched devices are more likely to contain security issues that haven’t yet been discovered by security researchers. The best choice is to buy products that have already been through several software updates.
3. When choosing which part of your life you’re going to make that little bit smarter, consider the security risks. If your home is the place where you store many items of material value, it would probably be a good idea to install a professional alarm system that can replace or complement your existing app-controlled home alarm system; or set-up the existing system in such a way that any potential vulnerabilities will not affect its operation.

