Trai chief fried over privacy, says no harm was caused
One user reportedly cloned his Aadhaar card which was accepted by Facebook and Amazon Cloud services as proof of identity.

Hyderabad: Twitterati had a field day showing Trai chairman R.S. Sharma how much personal data could be dug up after he made his Aadhaar number public on Saturday.
Tweeple dug up his mobile numbers, pictures, home address, date of birth and even chat threads and frequent flyer data using the Aadhaar number.
One user reportedly cloned his Aadhaar card which was accepted by Facebook and Amazon Cloud services as proof of identity. Using this, the person could use services of the platforms by impersonating Mr Sharma.
Internet researcher Anivar Aravind sent Mr Sharma Rs 1 via the government’s BHIM app to his bank account. He said the donation was to build government systems with better engineering to protect user privacy. “Just like pay to Aadhaar in BHIM, you can donate to his bank account without his consent using UPI as well. You can even use Tez app by Google (sic),” he tweeted.
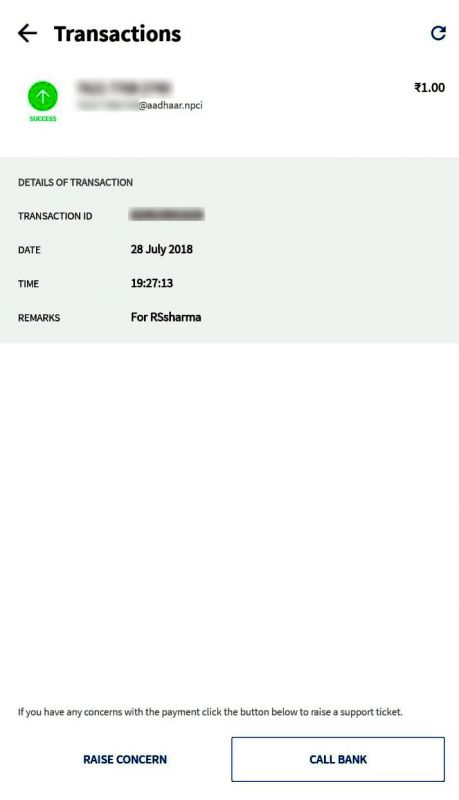 Screenshot of the Rs 1 transaction using BHIM app shared by Twitter user Anivar Aravind
Screenshot of the Rs 1 transaction using BHIM app shared by Twitter user Anivar Aravind
Mr Sharma remained unyielding and reiterated that the details shared on Twitter were available on the internet and there was no leak from the UIDAI as such, and no harm was caused to him wihch was his original challenge.
Because the phone number is also a communication address, criminals can work out means to a clone a person’s SIM card and steal their OTPs. It can also lead to creating misleading social media profiles like Facebook, Whatsapp and Twitter.
Mr Srinivas Kodali, independent security researcher, said, “This is what happens when Aadhaar is made mandatory. Even if a person doesn’t want Internet banking, they are being forced to opt in and it has become a default option. Anybody can add you and send money.”
“The important question to be asked is how it will harm. It may vary from gender to gender and person to person. For a not-so-tech savvy person, somebody may steal your land by using fingerprints. This is certainly not Aadhaar, the folks have made it a con. The onus is on government to ensure that risks are addressed as they are the ones who made it mandatory,” Mr Kodali said.
UIDAI said on Sunday said Mr Sharma’s details being put out on Twitter were not from the Aadhaar database or its servers. UIDAI said, “In today’s digital world through various search engines such as Google, personal data can be picked from different sources without Aadhaar and a profile can be made.
Aadhaar database is totally safe and has proven its security robustness over last eight years.”
Mr Sharma said he was merely “trying to dis-abuse the mis-information around Aadhaar”. But, even if Mr Sharma changes his phone number, people can still get his phone number because they have his Aadhaar number.
Experts said that such incidents are being reported because the government made Aadhaar mandatory without being aware of the risk mitigation strategy. Technical flaws cannot be covered under law as criminals do not follow the law.
French security researcher Robert Bapatiste who goes by the Twitter name Elliot Anderson, who termed Aadhaar as “privacy nightmare” said, “If your phone numbers, address, date of birth, bank accounts and others personal details are easily found on the Internet you have no privacy. With only an Aadhaar number, you can easily get the associated phone number. It’s working for all Indians, public servant or not (sic)”.
Experts said this vulnerability was important as the state recognises only Aadhaar. “Harm through Aadhaar may not seem straightforward. If Facebook can question government, they can act on this as well by bringing in a law. Government doesn’t say what the Aadhaar is. People will never know what kind of surveillance is being done on them, until it is done,” Mr Kodali said.
For instance in case of a person stalking a girl online, how she would know if someone is stalking? “A common man will remain unaware of the practices. People can take precautions only when they assume there is surveillance. For someone who is not tech-savvy, this information can be easily stolen using social engineering attacks and can be used to hurt him financially,” Mr Kodali said.
Another risky behaviour is of people sharing a lot of information on the Internet. A CID official from Telangana state said, “Everything is being put on the Internet. A lot of things which are supposed to be private are being put up knowingly or unknowingly. When people volunteer to give information to private companies which are using the data for giving advertisements, why fault a certain agency.”

