Hyderabad ISIS module in encryption shadow
The new Android app Amn Al Mujahid was launched to protect the members.
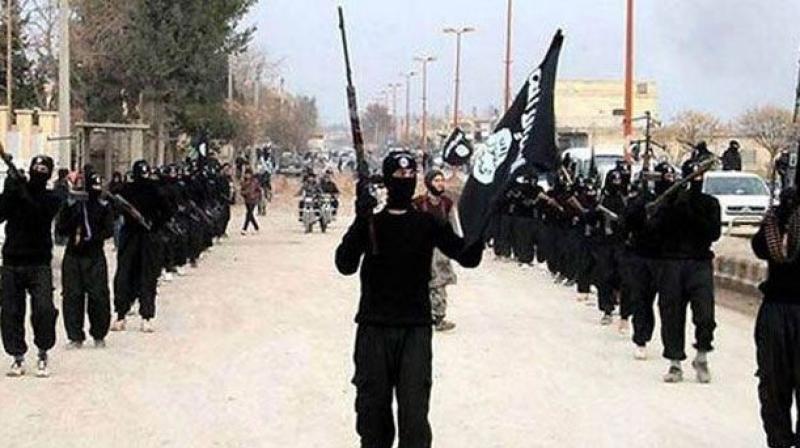
Hyderabad: “Protect yourself and your brothers, and encrypt your communications (as) the enemy is lying in wait,” ISIS mouthpiece alfajrtaqni.net had asked its fighters in June 2014, and they embraced the new encryption technology to evade the glare of law enforcement agencies. That’s what the eight ISIS suspects from Hyderabad too had been doing in their communications with ISIS handlers. Al-Qaeda in the Indian Subcontinent (AQIS) too had embraced the technology since the time they released their first issue of an English language magazine, Resurgence, in 2014.
Also, the Al-Fajr media centre, the media arm of ISIS, released a “highly secure” android app named Amn Al-Mujahid and published a 28-page instruction manual for the fighters, teaching them how to send emails through encryption. Official sources say ‘Al Fajr Technical Committee’ (FTC), which conceives and spreads the global terror outfit’s propaganda stuff, came up with the Android app Amn Al-Mujahid in June 2014, after enforcement agencies across the world strengthened their surveillance on ISIS fighters’ cyber indulgences.
While launching the new app and a new website, the FTC released a note, promising its fighters that the app was highly secure. “Your brothers in the technical committee of Al-Fajr (media centre) were able to write the ‘Amn Al-Mujahid programme. It is characterised by a strong encryption, and it is the best aid for the brothers since it follows the technological advancements. The programme has been provided with a 4096-bit public key [encryption]… making it the most secure system among the other [encryption] algorithms,” the note said.
Other online secret chat forums also had issued periodical instruction manuals for ISISI sympathisers in order to train them on how to remain anonymous and remove their digital footprints to evade the eyes of intelligence agencies. The training manuals included steps to modify the DNS, either manually or via a programme, and changing of IP addresses by spoofing etc.
The NIA charge-sheet on the Hyderabadi ISISI module stated that the members had installed Amn Al-Mujahid app in their phones and have extensively followed the training manuals to erase their digital footprints.

